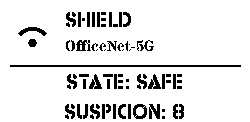
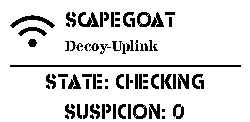
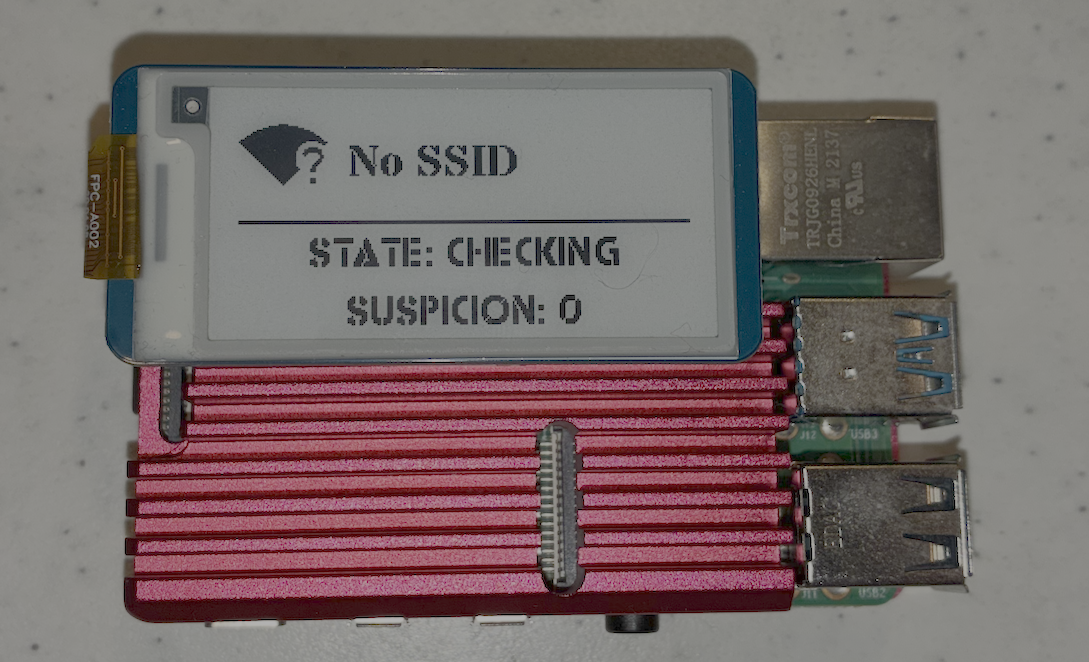
Azazel-Gadget
Portable Cyber Scapegoat Gateway for hostile networks.
A hacker who learned to attack — and chose to defend.
Move the target. Keep your endpoint invisible.
The network thinks it's talking to you. It's talking to Azazel.
NOT a VPN. NOT a travel router. NOT a promise of complete protection.